Member-only story
THM - Traverse
A writeup for the room Traverse on TryHackMe
Challenge your secure coding skills to restore a compromised website.
This room is about a compromised website that needs to be restored.
The website is compromised by an attacker who has uploaded a web shell and renamed a file used to manage the server.

https://tryhackme.com/room/traverse
Task 1 - Traverse
1. What type of encoding is used by the hackers to obfuscate the JavaScript file?
The website on port 80 doesn’t have much to offer.
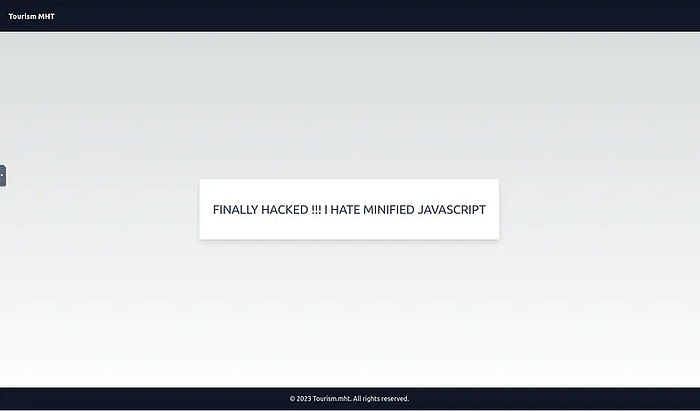
Even if there isn’t much to do here, there might be something in the code.
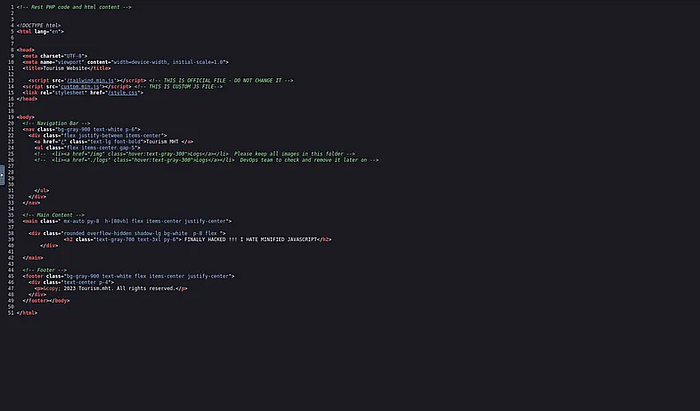
There is a custom Javascript file that may be of interest.

The content is obfuscated but can be identified as hexadecimal.
In fact, there are only pairs of numbers and letters between A and F, and each pair corresponds to an ASCII character.
2. What is the flag value after deobfuscating the file?
To deobfuscate the file, you can use any hex decoder, such as the one in CyberChef.
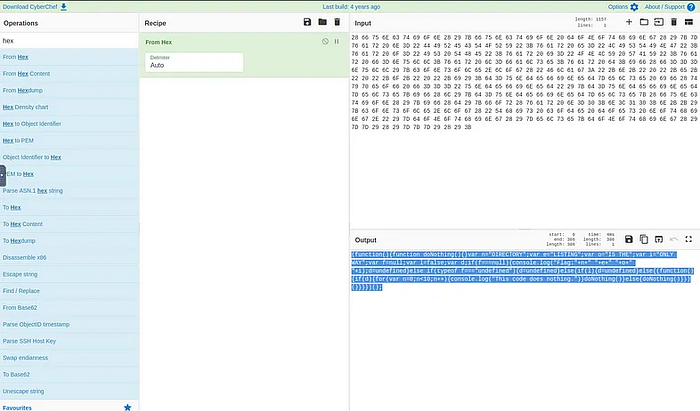
One way to see the result of the function is to run the code in the browser console.
